CYBERSECURITY
What is ISO/IEC 27032?
The term ISO/IEC 27032 refers to ‘Cybersecurity’ or ‘Cyberspace security,’ which is defined as the protection of privacy, integrity, and accessibility of data information in the Cyberspace. Therefore, Cyberspace is acknowledged as an interaction of persons, software and worldwide technological services.
The international standard ISO/IEC 27032 is intended to emphasize the role of different securities in the Cyberspace, regarding information security, network and internet security, and critical information infrastructure protection (CIIP). ISO/IEC 27032 as an international standard provides a policy framework to address the establishment of trustworthiness, collaboration, exchange of information, and technical guidance for system integration between stakeholders in the cyberspace.
Why is Cybersecurity important for you?
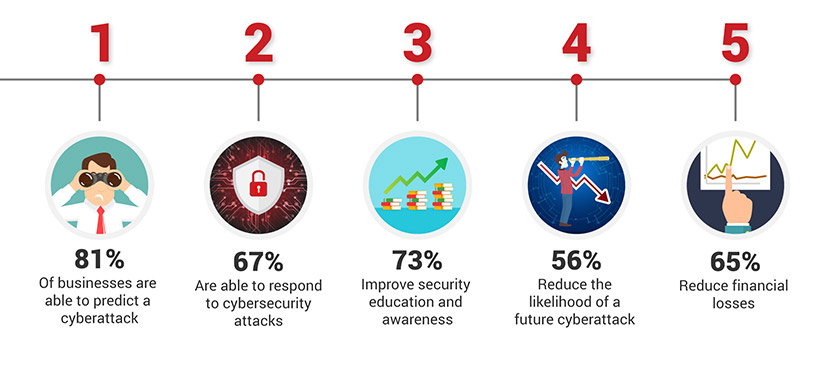
The ISO/IEC 27032 standard is essential for all businesses to utilize. The risk of security threats is increasing on a daily basis as we rely more on the cyberspace. However, the ISO/IEC 27032 standard provides guidelines regarding the protection and long-term sustainability of business processes. In addition, it equips individuals with the ability to develop a policy framework on which identifies the processes that are the most vulnerable to cyber-attacks; and that must be considered in order to ensure that business and clients will not be at risk.
ISO/IEC 27032 Cybersecurity training provides a real-world solution to individuals in protecting their privacy and organization data from phishing scams, cyber-attacks, hacking, data breaches, spyware, espionage, sabotage and other cyber threats. Being certified with ISO/IEC 27032 will demonstrate to your clients and stakeholders that you can manage and provide solutions to their cyber security issues.
Benefits of ISO/IEC 27032 Cybersecurity Management
Becoming a Certified ISO/IEC 27032 Cybersecurity Management enables you to:
- Protect the organization’s data and privacy from cyber threats
- Strengthen your skills in the establishment and maintenance of a Cybersecurity program
- Develop best practices to managing cybersecurity policies
- Improve the security system of organization and its business continuity
- Build confidence to stakeholders for your security measures.
- Respond and recover faster in the event of an incident
Contact us to start with the first step
PECB Certified ISO/IEC 27032 Training courses available
Learn more about Information Technology Security courses through the PECB ISO/IEC 27032 training course. Below you can find training that suits you best.
What is Cloud Security?
Cloud security is a set of strategies and practices used to secure cloud environments, applications, and data. Cloud security ensures the preservation of confidentiality, integrity, availability, and privacy of information hosted in a private, public, community, or hybrid cloud deployment model. It provides multiple levels of security controls in the cloud infrastructure that ensure data protection and business continuity.
Why is Cloud Security important for you?
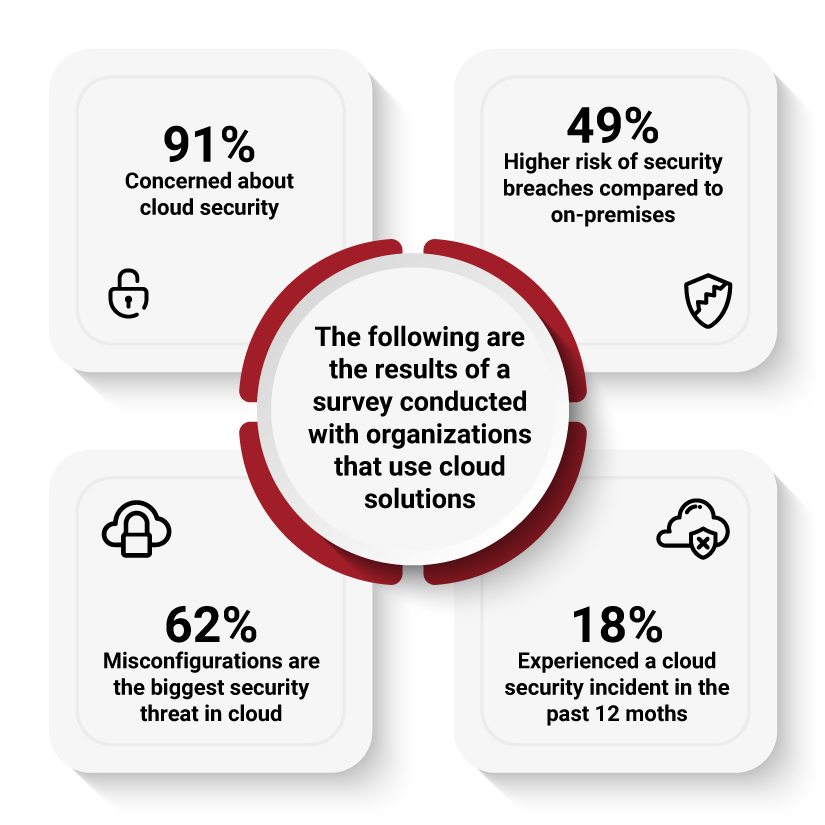
As the use of cloud computing grows constantly, so does the need to ensure cloud security. Data breaches and other forms of attacks happen mainly as a result of poor security practices, complicated controls, and misconfigurations. This makes cloud security essential to the effective operation of cloud services.
Organizations adopting cloud technology must ensure that the level of security of their cloud systems meets their requirements and complies with the applicable laws and regulations.
Implementing the guidelines of ISO/IEC 27017 helps cloud service providers and customers to establish, implement, and maintain information security controls related to cloud services. ISO/IEC 27017 provides additional guidance in selecting information security controls applicable to cloud services based on risk assessment and other cloud-specific information security requirements.
In addition, cloud service providers that process personally identifiable information (PII) in the cloud can implement the guidelines of ISO/IEC 27018 to meet the requirements of applicable regulations and legislation related to the protection of PII.
The Benefits of Cloud Security Certification
A PECB Cloud Security certificate demonstrates that you possess:
- A comprehensive understanding of cloud security concepts and principles
- The ability to identify and assess cloud-specific vulnerabilities and threats
- Practical knowledge to advise an organization in managing a cloud security program
- Knowledge on the tools and best practices needed to migrate to the cloud
- Knowledge needed to respond to and recover from a cloud security incident
- Skills needed to maintain and improve cloud security
The following are the results of a survey conducted with organizations that use cloud solutions:
How do I get started with Cloud Security Training?
We aim to help you expand your professional knowledge and advance your skills in cloud security. PECB experts are willing to help you with the certification process and with obtaining your PECB Certified Cloud Security Manager credentials.
Contact us to begin with the first step
PECB Certified Cloud Security Training Courses Available
Learn more about cloud security by attending the PECB Certified Lead Cloud Security Manager training course.
What is Penetration Testing?
Why is Penetration Testing important for you?
Benefits of Penetration Testing Certification
- Identify and analyze organization exposure to cybersecurity threats
- Improve your basic cybersecurity audit skills
- Learn the techniques, tools and hacking methods used by penetration testers
- Effectively manage time and resources
- Gain international industry recognition as a legal and ethical cybersecurity professional
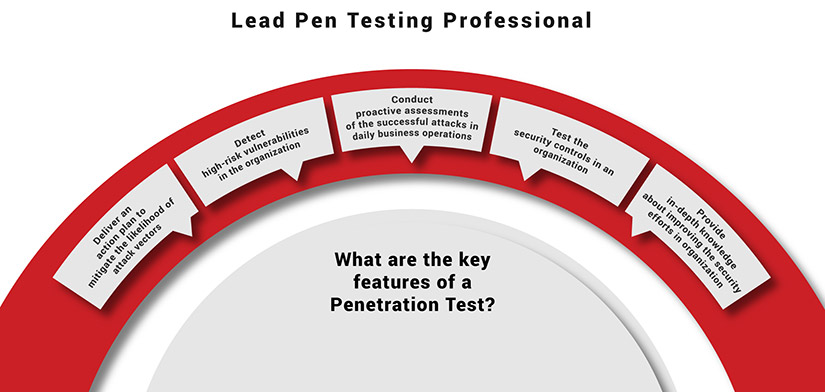
How do I get started with the Lead Penetration Testing Professional Training course?
A Lead Pen Test Professional is a training course designed for anyone with little or no experience in the field of penetration testing. This PECB training course will provide you with comprehensive theoretical instructions and hands-on training in the most innovative and advanced training environment. The PECB trainers are here to assure that you achieve the goal of becoming PECB Certified Lead Pen Test Professional.
PECB Certified Lead Penetration Testing Professional training course available
What is Ethical Hacking?
Ethical Hacking refers to the act of penetrating computer systems, networks or applications with the intention to exploit vulnerabilities that may lead to potential threats and risks. The main aim of Ethical Hacking is the improvement of the overall security of organizations by fixing the gaps and vulnerabilities found during penetration tests. Ethical hackers are allowed to use the same hacking techniques as malicious hackers with the permission of the organization which is to be tested.
Why is Ethical Hacking important for you?
Ethical Hackers are also known as White Hat Hackers because they use their expertise in hacking in order to improve the security of organizations by decreasing the number of vulnerabilities and security breaches. With the increase of the number of cyber-attacks, the global demand for ethical hacking services is constantly increasing as well. Globally known organizations chose to include ethical hacking in their security strategies, increasing the demand for Ethical Hackers across various industries. Moreover, experienced Ethical Hackers earn higher salaries than other professionals.
As an Ethical Hacker, you will prove that you possess the necessary expertise to support organizations detect their weaknesses, before a Black Hat Hacker does. Moreover, you will be able to demonstrate that you have the necessary skills to support the process of integrating penetration tests into the organization’s processes and ensure that the intended outcomes are achieved.
Benefits of Ethical Hacking
PECB Ethical Hacker Certificate will prove that you have:
- Mastered the concepts, approaches, standards, methods, and techniques used for the operation of an effective ethical hacking process
- Gained knowledge on the different attacks that can affect the security of an organization
- Obtained the necessary expertise to conduct a penetration test by using different tools and techniques
- Gained the ability to analyze the results of penetration tests and provide effective outcomes
- Higher chances of being distinguished or hired in the security career
- Strengthen your skills and personal qualities necessary to act with due professional care while conducting tests
- Acquired the ability to support organizations in the continual improvement process of their security
How do I get started with Ethical Hacking Training?
Interested in expanding your knowledge and advancing your skills on Ethical Hacking? PECB experts are here to ease the certification process and help you obtain the PECB Certified Ethical Hacker Credentials.
PECB Certified Ethical Hacking training courses available
Learn more about Ethical Hacking by attending the PECB Lead Ethical Hacker training course.
What is a SCADA system?
SCADA – Supervisory Control and Data Acquisition is an industrial system framework that includes both hardware and software architecture to control, monitor and analyze an industrial process. SCADA is an application software that enables managers, engineers, and industry operators, to supervise and communicate effectively with the working environment.
As an application software, SCADA is designed to assist industry experts in maintaining and improving industrial processes. Hence, the objective of SCADA is to collect real-time data, and store, process and generate reports for the complex industrial processes.
Why is it important to have a secured SCADA System?
SCADA is an essential tool that provides networking systems, communication and security technologies, and standards which are necessary to facilitate the maintenance of industrial processes. The application of technology is important for individuals to innovate and develop processes that will assist industries in the near future.
The aim of SCADA is to provide individuals with techniques to choose, plan and design technologies for improving the business processes and other utilities. In addition, SCADA will assist individuals to learn the required skills that are essential to plan, direct, operate and manage a project system in a working environment. The importance of SCADA is the automation system which allows the organization and individuals to anticipate risk uncertainties, lower investment, maintenance costs and study optimal responses to the continuity of industrial processes.
Benefits of SCADA Security Manager
By becoming a Certified SCADA Security Manager you will be able to:
- Develop a vulnerability assessment framework in SCADA Security
- Improve Access Control and Authentication Management
- Maximize your productivity and improve product quality
- Reduce your operating and maintenance costs
- Achieve long-term profitable investments
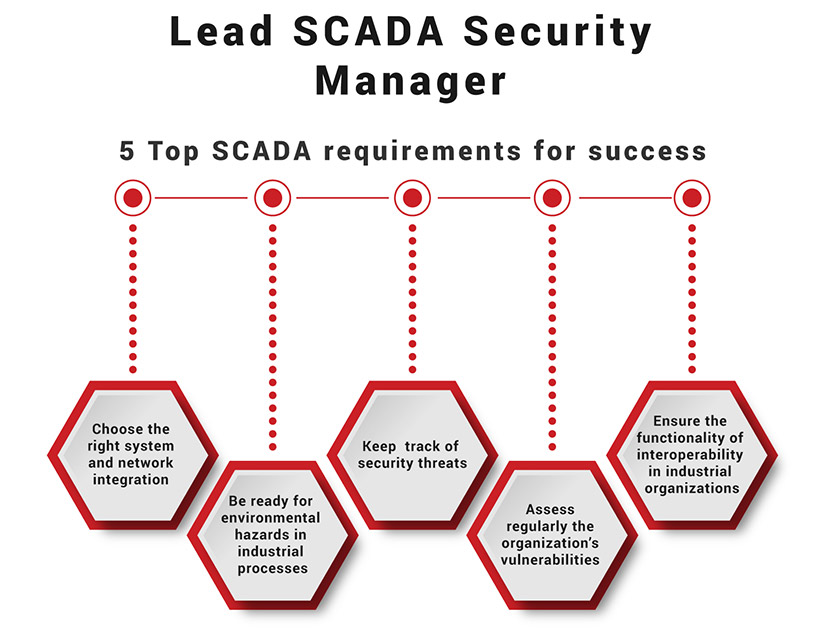
How do I get started with SCADA Training?
This PECB training course is designed to help managers, supervisors, and operators in the field of IT to discover how to configure the required tools and features for developing and organizing a SCADA projects in industrial processes. The PECB trainers are qualified and experienced professionals who are eager to share their knowledge and help you to achieve the goal of becoming a PECB Certified Lead SCADA Security Manager.
Contact us to start with the first step
PECB Certified Lead SCADA Security Manager training course available
By attending PECB training courses you will acquire the required knowledge and confidence to attain professional certification and enhance your career. Grab the opportunity and explore the following training course on how to become a Lead SCADA Security Manager.
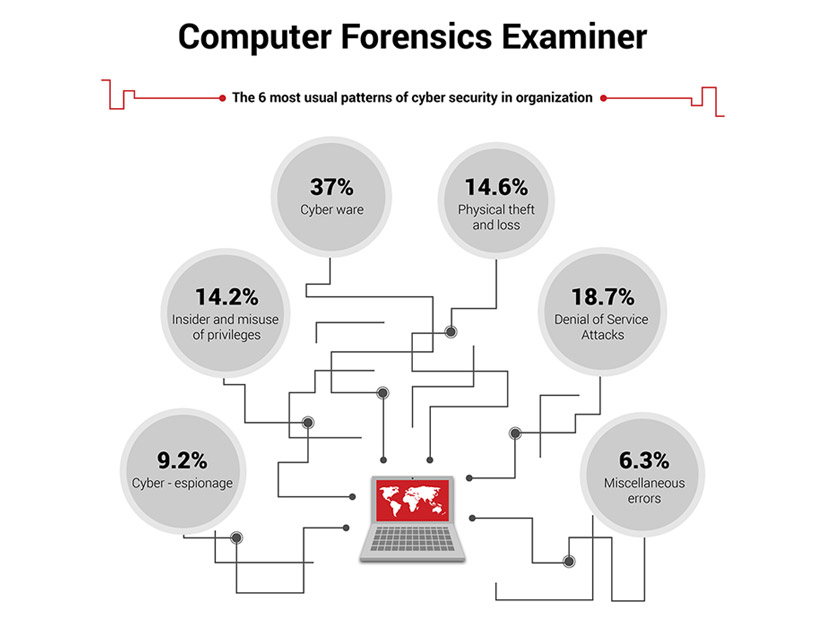
What is Computer Forensics?
Computer Forensics, also known as Cyber Forensics refers to the analysis of information in the computer systems, with the objective of finding any digital evidence that can be used for legal proceedings, but also to discover the cause of an incident. Computer forensics is the process of extracting data and information from computer systems to function as digital evidence for civic purposes, or in most cases to prove and legally impeach cybercrime.
The purpose of computer forensics is to provide forensic practices, legal processes, and ethical principles to assure reliable and detailed digital evidence that can be used for the courtroom needs. The objective of computer forensics is to guarantee a well-structured investigation and a follow-up of processes in order to resolve incidents and malfunctions in an organization.
Why is Computer Forensics important for you?
A forensics process is applied after the cyber attack or incident has occurred in order to collect and analyze the data to determine what happened, how did it happen and why did it happen? Computer forensics can be used as a tool to exploit backdoors that should be patched. A computer forensics investigation is a proficient mechanism that allows organizations’ to rationalize their time and immense financial impacts.
An internationally recognized computer forensic professional will be able to provide a detailed investigation of computer systems and assist the law enforcement authorities. Computer forensics’ provide you with the advantage of learning and practicing the latest comprehensive security methodologies of network systems, encryption technology, file operating systems, and criminal science.
Benefits of Computer Forensics
- By becoming Certified Computer Forensics Professional you will be able to:
- Understand the role of computer forensics in the business world.
- Support an organization to prevent incident occurrence
- Learn the prime forensic skills that can be applied in different situations.
- Improve your forensic techniques and tools to identify and respond to cybercrimes.
- Become an internationally recognized digital forensic professional
How do I get started with Computer Forensics Training?
You are about to take one of the most required training courses in the field of IT security. The PECB Computer forensics comprehensive training will provide you with outstanding skills that will help you to enhance your professional career. Our trainers are here to make sure that you achieve the goal of becoming a PECB Certified Professional on Computer Forensics.
Contact us to start with the first step
PECB Certified Computer Forensics training courses available
The available PECB program of Computer Forensics provides training courses that will assist you in learning the key concepts and practices involved in computer forensics processes. Check below to find the training course that suits you best.
What is Network Security?
The ISO/IEC 27033 series of standards consist of six parts designed to ensure network security of devices, applications, services, and end users. It covers securing communications between networks using security gateways, virtual private networks (VPNs), and wireless IP network access.
ISO/IEC 27033-1 is a mapping to the other parts. It provides an overview of the concepts and management guidance of network security by helping organizations identify and analyze network security risks and network security requirements.
ISO/IEC 27033-2 provides guideline on planning, designing, implementing, and documenting network security. It introduces the network security architecture, its requirements, and the design principles.
ISO/IEC 27033-3 illustrates network scenarios and their related threats, design techniques, and control issues. It helps organizations review technical security architecture, design, and security controls.
ISO/IEC 27033-4 provides guidelines on risks, design techniques, and controls of security gateways. It presents security gateways for securing information flows between networks.
ISO/IEC 27033-5 provides guidelines on risks, design techniques, and controls of virtual private networks (VPNs). It helps organizations select, implement, and monitor technical controls needed to connect remote users to networks.
ISO/IEC 27033-6 provides guidelines on risks, design techniques, and controls of IP wireless networks. It helps organizations select, implement, and monitor technical controls needed to secure communication between wireless networks. This part introduces wireless personal area networks (WPANs), wireless local area networks (WLANs), and wireless metropolitan area networks (WMAN).
Why is Network Security important for you?
A network is an essential component of the IT infrastructure which allows electronic communication and sharing of resources using network devices, protocols, services, interconnection, and infrastructure. Compromising any network infrastructure assets can lead to security and privacy breaches in communication.
Network security ensures the operation of the networks by protecting the network infrastructure and preserving confidentiality, integrity, and availability. An effective network security protects business processes.
The ISO/IEC 27033 series can help organizations plan, design, and implement network security by creating a secure environment and protecting virtual networks and physical devices, data, and proprietary information.
The Benefits of Network Security Certification
- Improved network security
- Enhanced protection of information system networks and personal data from unauthorized access
- Reduced number of security incidents and their impacts
- Reduced slow networks and downtime
- Boosted satisfaction of customers and interested parties
- Increased international recognition
Top network characteristics that benefit from an ISO/IEC 27033 implementation

How do I get started with ISO/IEC 27033 Training?
PECB ISO/IEC 27033 training courses are part of a global network of qualitative training. They can help expand your professional knowledge and advance your skills in network security. PECB experts will help you with the certification process.
Contact us to begin with the first step
PECB Certified ISO/IEC 27033 Training Courses Available
Learn more about network security by attending the PECB Certified ISO/IEC 27033 Lead Network Security Manager training course.
What is CMMC?
The Cybersecurity Maturity Model Certification (CMMC) framework is a verification mechanism designed to measure the organizations’ maturity regarding the protection of unclassified information such as Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). CMMC is a new set of cybersecurity standards that encompasses various cybersecurity standards, references, and other best practices. It comprises a number of processes and practices which are mapped across five cumulative certification levels.
The CMMC model is developed and managed by the Department of Defense (DoD) and is considered to be the DoD’s response to potential compromises of sensitive information that resides on Defense Industrial Base (DIB) systems and networks. CMMC Accreditation Body (AB), on the other hand, is the sole authoritative source for the operationalization of CMMC assessments and training.
Why is CMMC Important for You?
As in any other area, the large number of security incidents has also affected the Defense Industrial Base and the supply chain of the Department of Defense (DoD). The DoD is aware that, in order to decrease the risk related to national economic security and in general the national security, it should be focused on protecting its unclassified information. Therefore, the DoD released the CMMC framework which assesses and enhances the cybersecurity posture of organizations throughout the DoD contractor community. Since CMMC is a cybersecurity standard, the CMMC certification will eventually be required for all DoD contractors, including small businesses, commercial item contractors, and other suppliers. The CMMC training courses will help you acquire knowledge on CMMC domains, practices, and processes and understand how they may be applied within the DoD supply chain. In addition, CMMC training courses will help you understand the CMMC certification process and prepare you for your role in the CMMC-AB ecosystem.
Benefits of the CMMC Training Courses
The Certified CMMC training courses will help you to:
- Understand the basic concepts, definitions, and approaches of the CMMC model
- Understand the CMMC domains, capabilities, processes, and practices applicable for each CMMC maturity level
- Gain the ability to interpret the CMMC requirements in the specific context of an organization
- Understand the CMMC assessment methodology and process across all CMMC levels
- Obtain the necessary expertise to support an organization in implementing and managing the requirements of the CMMC model
How Do I Get Started with CMMC Training Courses?
Our training courses are delivered by experienced trainers which aim to help you extend your professional knowledge and advance your skills on CMMC requirements implementation and assessment. PECB is also an approved organization as a Licensed Partner Publisher (LPP) for CMMC, and it will develop training curricula based on the CMMC-AB’s Body of Knowledge.
PECB experts will help you to facilitate your certification process and help you obtain one of the PECB certifications.
Contact us to begin with the first step
PECB Certified CMMC Training Courses Available
Learn more about CMMC by attending the Certified CMMC training courses. During the training course, you will learn all the necessary tools and approaches that will enable you to perform your role in the CMMC-AB ecosystem.
For additional information, please contact us at info@isotrainings.in







